Your VP of Sales walks into your office looking frustrated.
"I just lost a deal. Six-month sales cycle. $400K ARR. We were the better product. They went with the competitor."
You ask why.
"Security. They said the competitor's security posture gave them more confidence."
You're confused. You have SOC 2. You do annual pen testing. You're compliant with everything. What does the competitor have that you don't?
The answer, usually, isn't better security. It's better communication of their security.
Here's a sad truth that most people don't want to hear: Your actual security posture matters much less than your perceived security posture when it comes to winning deals, retaining customers, and commanding premium pricing.
I know that's going to trigger some purists. "Security should be about real controls, not marketing!" I agree. In a perfect world. But we don't operate in a perfect world. We operate in a world where:
- Buyers can't actually evaluate your technical security (they're not security experts) (e.g., The Market for Silver Bullets)
- They're making decisions based on trust signals and social proof
- Your competitor is actively positioning their security as a differentiator
- Security questionnaires are being filled out by procurement teams who are looking for the "right" checkboxes
If you have strong security but can't articulate it externally, you're probably leaving money on the table. If your competitor has adequate security but positions it brilliantly, they're winning deals you should have won.
To be clear, this isn't about lying or exaggerating. This is about taking the security work you're already doing and translating it into language that creates competitive advantage.
Let me show you how.
Check out our Security Positioning Template Library → https://adversis.github.io/security-positioning-library/
The Security Positioning Gap
Most companies have a massive gap between their actual security posture and how they communicate it externally:
What you have
- Annual penetration testing by reputable firms
- SOC 2 Type II certification
- Incident response procedures
- Encryption at rest and in transit
- Regular security training
What your website says:
"We take security seriously."
What your competitor says:
"Enterprise-grade security validated through regular penetration testing by independent security firms, SOC 2 Type II certified with zero audit exceptions for three consecutive years, 24/7 security operations center, and mature internal engineering practices. Our security posture is independently benchmarked in the top 10% of companies our size."
Same security. Completely different positioning. And your competitor just won the deal.
The External Security Communication Framework
Let's break down how to position your security externally across different channels and audiences. Less about “we’re secure” and more about weaving security credibility into every customer touchpoint.
Level 1: Your Public Security Presence (Website/Marketing)
Where this lives
- Dedicated security page on your website
- Product pages (security as a feature)
- About/Company pages (security as company value)
- Sales collateral and one-pagers
What to include
1. Certifications and Compliance (Trust Badges)
Don't just list them. Context matters.
🚫 Weak positioning:
"We are SOC 2 Type II certified."
☑️ Strong positioning:
"We maintain SOC 2 Type II certification with annual audits conducted by [reputable audit firm]. Our most recent audit completed in [month/year] with zero exceptions, demonstrating our commitment to security, availability, and confidentiality controls."
Why this works: You're not only claiming compliance—you're providing specificity (who audited, when, what the results were) that signals transparency and credibility.
What you can say about your pen test (from our previous articles in this series):
🚫 Weak positioning:
"We conduct regular penetration testing."
☑️ Strong positioning:
"We conduct comprehensive penetration testing by independent third-party security firms on a [annual/quarterly/continuous] basis. Our most recent assessment was completed in [quarter/year], with all critical and high-severity findings remediated and independently validated."
Even stronger if you can add context:
"Our penetration testing program includes both scheduled annual assessments and targeted testing before major product releases, ensuring security is validated throughout our development lifecycle."
The key principle: Specificity builds credibility. "Regular testing" is vague. "Quarterly testing by independent firms with validated remediation" is specific and impressive.
2. Your Security Team (Human Trust Signals)
Share if you have dedicated security resources. It's a competitive advantage.
🚫 Weak positioning:
"Our team includes security experts."
☑️ Strong positioning:
"Our dedicated security team includes [number] full-time security engineers with backgrounds in [relevant experience: offensive security, incident response, compliance, etc.], led by our CISO who brings [X years] of experience in [relevant background]."
If you're small and don't have a big security team:
"While lean, our security function is led by [name/title], who works directly with our engineering and infrastructure teams to integrate security into everything we build. We augment our internal expertise by partnering with [reputable firm] as a comprehensive sparring partner, including attack path mapping and regular penetration testing. We also maintain active relationships with the security research community through our bug bounty program."
Why this works: You're acknowledging reality while demonstrating that security is taken seriously at the leadership level. Small companies that position security thoughtfully often beat larger companies that treat it as an afterthought.
3. Security Architecture and Controls (Technical Trust Signals)
This is where you translate your actual security controls into customer-facing language.
These need to be technical enough to satisfy technical evaluators, but clear enough for non-technical decision-makers.
A useful framework
Infrastructure Security:
"Our infrastructure is built on AWS/Azure/GCP with security-hardened configurations, automated vulnerability scanning, and continuous security monitoring. All infrastructure changes go through our security-reviewed change management process."
Application Security:
"We integrate security throughout our development lifecycle, including threat modeling, automated security testing (SAST and DAST) in CI/CD, code review requirements before production deployment, and independent penetration testing before major releases."
Data Security:
"We implement role-based access controls, data segregation between customers, and regular access reviews. Strictly controlled and limited access to all production data. All data handling complies with [GDPR/CCPA/relevant regulations]. Customer data is encrypted at rest using AES-256 and in transit using TLS 1.2+."
Access Management:
"We enforce multi-factor authentication for all employee access to production systems internally, implement least-privilege access principles, conduct quarterly access reviews, and maintain full audit logs of system access."
Incident Response:
"We maintain a 24/7 incident response capability with defined escalation procedures, annual incident response tabletop exercises, and breach notification procedures aligned with [relevant regulations]. Our mean time to detection and response is continuously monitored and improved."
Notice that we’re describing what you actually do, but in language that demonstrates maturity and sophistication. Not exaggerating, just not underselling.
4. Transparency Signals (Confidence Builders)
These are the signals that say "we're so confident in our security that we're willing to be transparent about it."
Bug Bounty Programs:
If you have one, promote it:
"We operate a public (or private) bug bounty program, welcoming security researchers to help us identify and resolve potential vulnerabilities. We annually budget to compensate researchers who have helped us maintain our security posture, with an average time to resolution of [X days] for validated findings."
And if you don't have a public bug bounty, since they can be time consuming and not without cost, you can still signal openness:
"We maintain a coordinated disclosure policy and welcome security researchers to report potential vulnerabilities through [email/portal]. All validated reports are acknowledged within 48 hours and resolved according to severity."
Security Roadmap Transparency:
"We publish an annual security roadmap outlining our planned security investments and improvements. [Link to relevant location]."
Incident History (Only when very mature):
If you've had a security incident that you handled well, consider being transparent about it. Cloudflare is often held in high regard here. If you’re obscuring details or information to protect inadequacies, consider not sharing publicly.
"We identified and resolved a [description] security issue affecting [scope]. We immediately [actions taken], notified affected users within [timeframe], and implemented [preventive measures]. We believe transparency about security incidents and our response demonstrates our commitment to continuous improvement."
Nobody expects you to be perfect. They expect you to be responsible. Controlled transparency about how you handle security, including incidents, builds more trust than claiming you've never had an issue.
Level 2: Sales Enablement Materials
Your sales team is on the front lines, answering security questions from prospects. They need materials that position your security as a competitive strength, not just a checkbox.
A Security One-Pager
Create a single-page document (PDF) that your sales team can send to any prospect who asks about security. Structure it like this:

Header
- [Company name] Security Overview
- Date of last update
- Version number
Certifications & Compliance
- List all relevant certifications with dates
- Mention audit firm for credibility
- Include compliance frameworks you adhere to
Security Testing & Validatio:
- Penetration testing cadence and most recent date
- Vulnerability management approach
- Bug bounty program (if applicable)
Data Protection
- Encryption standards (at rest and in transit)
- Data residency options (if relevant, e.g., GDPR)
- Backup and disaster recovery approach
Access & Authentication
- Employee access controls (MFA, least privilege)
- Customer authentication options (SSO, MFA)
- Audit logging capabilities
Incident Response
- Incident response capability (24/7 monitoring, defined procedures)
- Breach notification commitment
- Contact for security issues
Security Team
- Brief description of security leadership
- Team size/structure (if impressive)
- How to contact security team
Footer
"For detailed security documentation, including our SOC 2 report, penetration test executive summaries, or security questionnaire responses, please contact [email]."
Pro tip from our last article: If you've been doing pre-launch security testing (as discussed in the Product Launch section), you can include:
"All major product releases undergo independent security testing before public availability, ensuring vulnerabilities are identified and resolved before customer exposure."
Most companies can't say that.
The Security FAQ Document
Create a comprehensive FAQ document that answers the 20-30 most common security questions your sales team gets asked. This becomes a living document that your sales team can pull from when responding to prospects.
Categories
- Data Security & Privacy
- Access Control & Authentication
- Compliance & Certifications
- Vulnerability Management
- Incident Response
- Business Continuity
For each question
- Question (exactly as prospects ask it)
- Answer (clear, specific, honest)
- Supporting documentation available (if applicable)
Example
Q: How often do you conduct penetration testing?
A: We conduct comprehensive penetration testing annually by [independent security firm], with additional targeted testing before major product releases. Our most recent annual assessment was completed in [month/year], with all critical and high-severity findings remediated within [timeframe]. We also maintain a bug bounty program for ongoing security validation. We're happy to provide executive summaries of our pen test results under NDA for qualified prospects.
Notice: Specific, credible, and ends with an offer to provide more detail. That's how you build trust.
For example
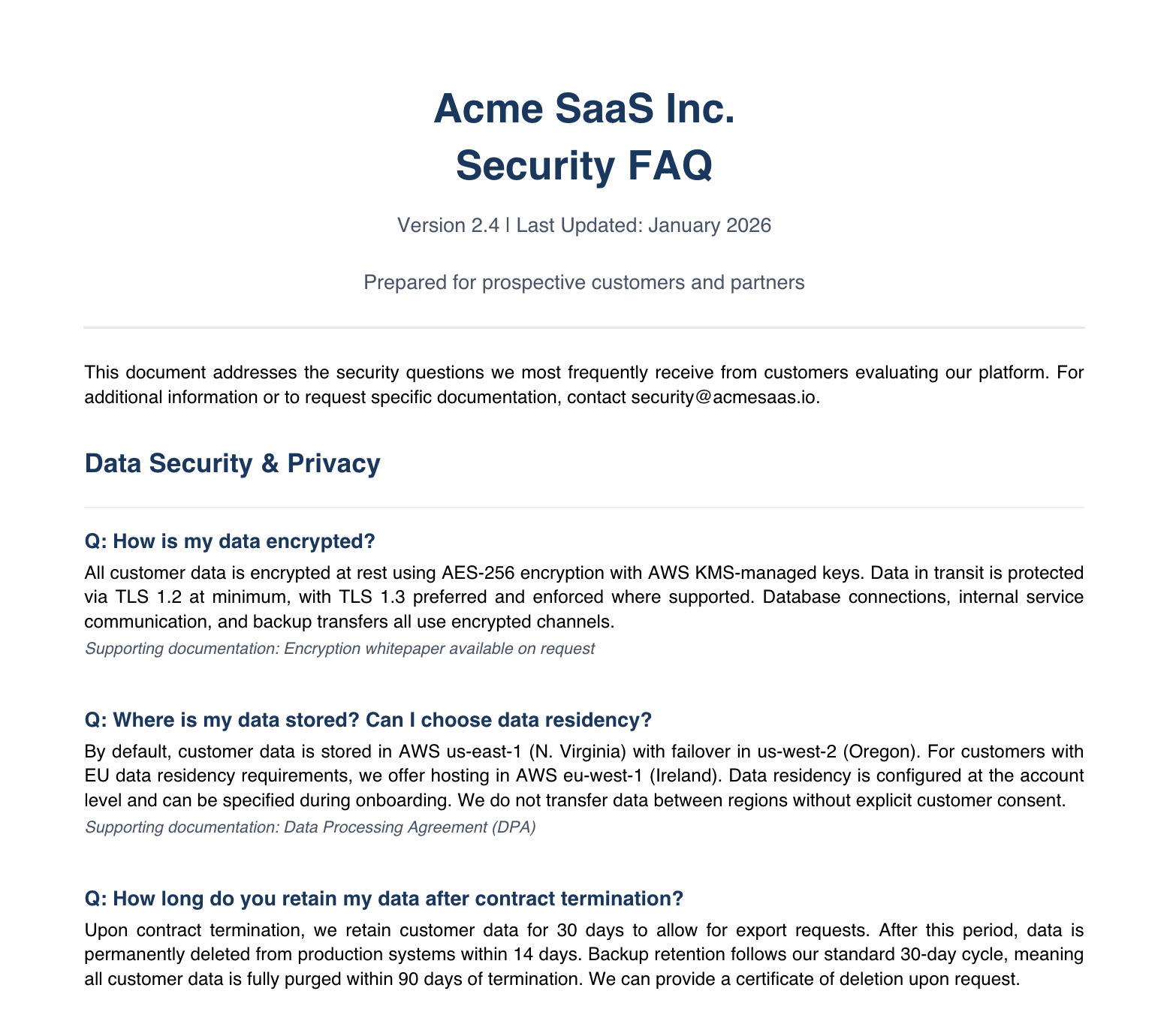
Again, these should represent reality, and you should be able to speak confidently about the answers and provide proof via screen share, screenshots, and conversations with a prospective customer’s security team. Especially as AI-generated answers can look so polished, jaded security teams and CISOs will, unfortunately, want to challenge them.
If you have a Trust Center, make these documents available there.
Level 3: Security Questionnaires (Deal Accelerators or Killers)
Enterprise buyers send security questionnaires. They're painful, time-consuming, and critical to closing deals. Most companies treat them reactively: a questionnaire arrives, the security team scrambles to answer 200 questions, it takes 2-3 weeks, and momentum, need, or budget dies.
A more strategic approach
1. Build a Master Questionnaire Response Database
Take the 10 most recent security questionnaires you've received. Compile every unique question into a master database (spreadsheet or dedicated tool). For each question, write your authoritative answer once.
Now, when new questionnaires arrive, you're copy-pasting from your database, not rewriting answers. This turns a 3-week process into a 3-day process.
Categories in your database
- Company information
- Certifications & compliance
- Data security
- Network security
- Access control
- Physical security
- Vendor management
- Incident response
- Business continuity
- Application security
- Employee security
2. Create "Tier 1" Auto-Responses
For deals below a specified size threshold, create a pre-filled "standard security questionnaire response" document that covers 80% of the most common questions. Send it proactively when security questions come up: "Here's our standard security questionnaire response. If you have additional questions not covered here, let me know."
This positions you as prepared and professional, and massively reduces your team's workload. Unfortunately, it seems everyone wants answers returned in their requested format or document.
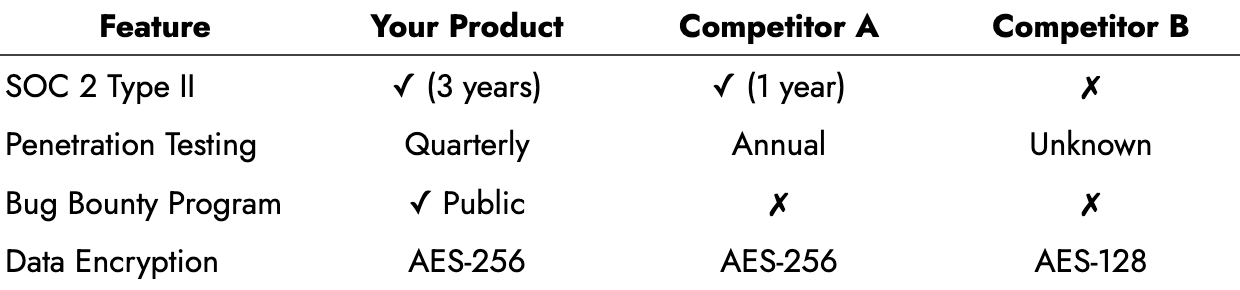
3. Use Security Questionnaires as Competitive Positioning
Most companies answer questionnaires defensively, trying to check boxes. Smart companies use questionnaires offensively, to differentiate.
For Example
Question: "Do you conduct penetration testing?"
Defensive answer: "Yes, annually."
Competitive answer: "Yes. We conduct annual comprehensive penetration testing by independent third-party security firms, plus targeted testing before major product releases. Our most recent annual test was completed in Q2 last year with all critical/high findings remediated and validated. This exceeds the security testing cadence of most vendors in our space."
That last sentence—"this exceeds the security testing cadence of most vendors in our space"—is competitive positioning. You're helping the prospect understand you're better than alternatives.
Pro tip from earlier in our series: Remember the "Business Enablement" budget bucket? This is why it matters. If your sales team is consistently losing deals because competitors have better security positioning, that's a revenue impact that justifies security investment. Track it:
"Last quarter, we lost 3 deals where security was cited as a differentiator for competitors. Total pipeline impact: $900K. Investment in quarterly pen testing and security certifications would cost $150K annually and would enable us to position competitively. That's a 6:1 return if it saves just one deal per year."
Level 4: Proactive Security Marketing
The most sophisticated companies don't wait for prospects to ask about security. They proactively make security part of their brand and market positioning.
Security-Focused Content Marketing
Create content that positions you as security-mature.
Blog posts
- "How we approach security: Inside our security testing program"
- "We were just SOC 2 certified - what it means for you"
- "Our security roadmap: Investments we're making to protect customer data"
Case studies
- "How [Customer] achieved their security compliance requirements using our platform"
- "Security at scale: How we maintained our security posture while growing 10x"
Webinars
- "Security best practices with our platform for [your industry]"
- "How to evaluate vendor security: A buyer's guide"
You're demonstrating security expertise publicly. When prospects research you, they find evidence that security is a core competency, not an afterthought.
Security as Product Marketing
Integrate security into your product marketing, not just your compliance page.
On product pages
- "Built with security-first architecture"
- "Validated through independent penetration testing"
- "SOC 2 certified from day one"
In product demos
Train your sales team to naturally weave in security proof points:
- "And you'll notice here [during demo] we enforce MFA for all administrative access with phishing-resistant methods as default..."
- "This audit log shows you exactly who accessed what and when—full transparency for your compliance needs..."
- "Our encryption approach means your data is protected both in transit and at rest, and our access to any data is extremely restricted..."
In product comparison charts
Security-Focused PR
When you achieve security milestones, treat them as PR opportunities.
Press releases for
- New security certifications achieved
- Expansion of security team/hiring notable security leader
- Launch of bug bounty program
- Significant security investment or partnership
For example
- "[Company] Achieves SOC 2 Type II Certification, Reinforcing Commitment to Customer Data Security"
- "[Company] Launches Public Bug Bounty Program, Invests $500K in Security Research Community"
- "[Company] Hires Former [Notable Company] Security Leader as CISO"
All market positioning opportunities.
Level 5: Customer Communication (Retention Plays)
Your existing customers care about security, too. Regular security updates build trust and reduce churn.
Annual Security Updates
Send an annual email to customers summarizing your security posture and recent improvements:
Subject: "[Company] [Year] Security Update"
"We know security is a top priority for our customers. Here's a summary of our security activities last year:
✓ Completed quarterly penetration testing with zero critical findings
✓ Remediated 8 medium-severity findings identified in testing
✓ Upgraded infrastructure to latest security patches
✓ Conducted security awareness training for all employees
✓ Maintained SOC 2 Type II compliance with zero audit exceptions
What we're working on this upcoming year:
- Implementing enhanced logging and monitoring capabilities
- Expanding our bug bounty program scope
- Additional third-party security certifications
As always, if you have security questions or concerns, contact our security team. Thank you for trusting us with your data."
Why this works
- Demonstrates ongoing security investment
- Builds confidence in your security program
- Reduces security-related churn
- Creates advocates (customers forward these to their security teams)
Security Incident Communication (As Necessary)
If you have a security incident, how you communicate it externally matters enormously. As mentioned earlier, Cloudflare is often highly regarded here. If you’re obscuring details or information to protect inadequacies, consider not sharing publicly. If you do, and with legal’s involvement and approval:
1. Acknowledge quickly and transparently
"We identified a security issue on [date] affecting [scope]. We're investigating and will provide updates as we learn more."
2. Provide factual updates
"Update: We've determined that [X user accounts/Y data types] were potentially affected. We have [contained/resolved] the issue. Affected users will be notified directly."
3. Explain your response
"We immediately [actions taken]. We've engaged [third-party forensics firm] to conduct a thorough investigation. All affected users have been notified and we're offering [remediation: credit monitoring, etc.]."
4. Share lessons learned
"Post-incident analysis identified that [root cause]. We've implemented [preventive measures] to prevent recurrence. We've also [additional security improvements]."
Pro tip from Topic 3: If you've been doing proactive pen testing (especially the "Industry Response" scenario from Topic 1), you can reference it in incident communications:
"While no security program is perfect, we maintain a rigorous security testing program including quarterly penetration testing and a public bug bounty program. This incident represents a gap in our controls that we've now addressed through [improvements]."
This contextualizes the incident: Yes, something happened, but we have strong security practices overall and we've learned from this.
What You Can (and Shouldn’t) Say Publicly
Let's be clear about boundaries. There are things you should say, things you can say carefully, and things you should never say.
Things you should say publicly:
- Certifications you hold (SOC 2, ISO 27001, PCI, HIPAA, etc.) with dates
- Testing cadence (annual, quarterly, continuous)
- That you conduct penetration testing by independent firms
- That you've remediated findings (without specifics)
- General security architecture (encryption standards, access controls)
- Bug bounty program existence and general stats
- Size/structure of security team
- Compliance frameworks you follow
Things you can say with care:
- Names of pen test vendors (check with them first)
- Executive summaries of pen test results under NDA with qualified prospects
- Benchmarking data if you have it ("We exceed industry average security posture")
- General finding categories from pen tests ("We test web applications, APIs, infrastructure, and cloud configuration")
Things you shouldn’t say publicly:
- Specific vulnerabilities found in pen tests (even historical ones), open-source excluded of course
- Detailed technical architecture that could inform attackers, unless you have a mature ecosystem and detection and response capabilities
- Specific security controls in granular detail (locations of security devices, specific monitoring approaches)
- Customer-specific security configurations
- Anything that suggests your security is "perfect" or "unhackable" (that's a challenge, and it's not true)
Transparency builds trust. Over-disclosure creates risk. There’s a balance that demonstrates your security maturity without providing a roadmap for attackers.
The Bottom Line
You're already doing security work. Pen tests. Compliance. Controls. Training.
The question is: Are you getting full value from that work?
If prospects don't know about your security posture, it might as well not exist from a competitive standpoint. If your sales team can't articulate your security advantages, you're losing winnable deals. If customers don't hear about your security improvements, they're not building trust and loyalty.
Security positioning isn't about lying or exaggerating. It's about making sure the security work you're doing translates into:
- Competitive differentiation in sales
- Customer confidence and retention
- Premium pricing justification
- Faster sales cycles
The companies winning on security aren't necessarily the most secure. They're the ones who are secure and know how to communicate it.
Your penetration testing—if done strategically as we've discussed through this series—gives you concrete proof points for external positioning:
- Testing frequency (annual, quarterly, continuous)
- Independent validation by reputable firms
- Remediation track record
- Year-over-year improvement
- Pre-launch testing discipline
Don't let that work sit in a report nobody sees. Turn it into competitive advantage.
Want help building your external security positioning strategy? We created a Security Positioning Audit that evaluates your current external security presence across 50 criteria, benchmarks you against competitors, and provides a prioritized roadmap for improvement. It includes templates for security pages, one-pagers, questionnaire responses, and customer communications.
Check out our Security Positioning Template Library → https://adversis.github.io/security-positioning-library/
About This Series
This is part 4 of our Strategic CISO Series—a collection of guides focused on turning operational security work into strategic wins.
Read the series
- Part 1: The Board Deck Penetration Test: Timing Your Security Assessment for Maximum Strategic Impact
- Part 2: How to Say 'We Need More Security Budget' Without Saying 'We're Currently Insecure'
- Part 3: The Pre-Mortem Pen Test: Using Security Assessments to Accelerate M&A, Funding, or Major Launches
- Part 4: From Checkbox to Competitive Advantage: Positioning Your Security Posture Externally (you are here)
Coming up
- Part 5: The Quarterly Security Win: Manufacturing Visible Victories When Your Job Is Preventing Invisible Disasters
Written for security leaders who want security to be a business driver, not just a compliance function. If this resonates, we'd love to hear from you.





